Best Security Awareness Ideas 2023
Activities & Resources for National Cyber Security Awareness Month (NSCAM)
October is a special time of year in the information and cyber security calendar as it marks the widely recognised Cyber Security Awareness Month. An important month in which governments and private industries the world over collaborate in raising awareness around important security issues and help protect data.
Originally started in 2004 by the US Department of Homeland Security, (National) Cyber Security Awareness Month is this year promoting the theme of See Yourself in Cyber.
Placing the emphasis on the participation and efforts of the individual, as well as highlighting the importance of addressing avoidable human error, this year's Cyber Security Awareness Month is a great opportunity to engage employees and level-up your business security culture.
With the theme of See Yourself in Cyber in mind, below are Hut Six's top five campaign ideas for your business or SME in 2023.
Password Refresh
As a foundational element of information and cyber security, maintaining strong passwords is an essential for organisations and individuals alike; though the unfortunate reality is that '123456' still remains the most common password found within breaches.
That's why we propose launching a password refresher campaign this October. A chance, perhaps even an hour or two, for all users to assess their almost certainly massive collection of passwords and take the time to ensure that they meet an acceptable standard of security.
Consider, for instance, the aforementioned password of '123456'. With today's standards of computing, this password would take only a fraction of a second for cyber criminals to crack. What about something more complex, such as 'ElectricMonkey'? Again, barely a few seconds are required for that account to be compromised.
For a simple a secure way of generating strong passwords, we recommend the 'four random words' method. By combining only four unconnected words, users can without the help of a password generator, create passwords which are essentially unbreakable.
For example, according to this handy password checker, 'ConductorMassExperimentBelt', a password created with our simple technique, would take over ten thousand centuries for the average home computer to brute force. Safe to say, a lot more secure than six sequential digits.
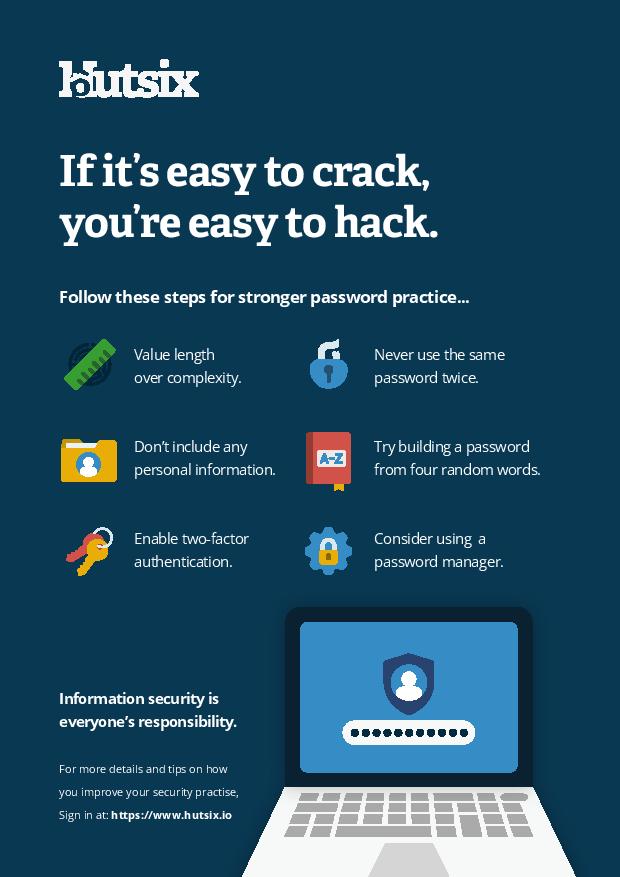
Posters
Perhaps not the most novel resource, posters and other visual assets are still great ways of regularly reminding users of information security topics and potential threats that they encounter on a daily basis.
Below we've included several posters to get you started, covering a select few topics which represent some of the most common and avoidable security threat vectors, including password security and phishing.


Cyber Champions
As social creatures, it is not just the information contained within a message which impacts us. In fact, who it is that communicates a message significantly influences how we response. Accordingly, finding the right individuals to promote the message of cyber security can be key in affecting change this Cyber Security Awareness Month.
Electing respected and knowledgeable employees to champion your cyber security efforts this year, your cyber champions can act as representatives for this year's awareness month; answering questions, sharing stories, and highlighting the achievements of other users are all great ways of engaging individuals in important cyber topics.
With multiple studies finding that by sharing information about the compliance of users increases the likelihood of other users complying with security policies themselves, the power of social influence, or as psychologists term it social proof, is very much worth taking into consideration when thinking about how to make learning more social.
Leader Boards
Again, utilising the power of social learning and of a healthy competitive spirit, leader boards are a simple and effective method of engaging users to actively participate in information and cyber security compliant behaviour.
With the option of either company-wide, or department specific, how you organise your leader board system will depend on your organisation and personal preferences, though we recommend that for your scoring as reliable metrics as possible are used.
Whether your points or scoring system is based on a stand-alone quiz, or on a broader month-long simulated phishing campaign, leveraging users' competitive nature could even be boosted by offering rewards for those who achieve particularly impressive results.
For those wishing to find out more about simulated phishing campaigns, and how they can not only help to protect your organisation with easily automated and customisable phishing emails, but also provide valuable data on user behaviour, click here to learn about Hut Six's phishing simulator.
Social Engineering Tests
For those not in the know, the term social engineering covers a wide variety of possible attacks. Including elements from both physical and digital/cyber security, social engineering is most simply defined as malicious actions designed to exploit human behaviour.
For example, in a recent experiment conducted by a Google research team, around 300 USB drives were scattered across a university campus. Although in this case the USB drives were loaded with harmless software designed to track behaviour, the devices could have just as easily contained dangerous forms of malware.
Leveraging the curiosity, and in some cases the altruistic urge to track down an owner (a social engineering method known as baiting), this experiment found that over 45% of drives were plugged in and had files examined. A simple, yet very effective method cyber criminals could exploit to steal sensitive data.
With some larger companies opting to hire external companies specialised in penetration testing, this Cyber Security Awareness Month can be your organisation's chance to examine its resilience against some common social engineering attacks.
To find out more about social engineering methods why not check out our blog 4 Ways Criminals Exploit Human Behaviour covering not only baiting, but also other methods including pretexting and quid-pro-quo.
Security Awareness for your Organisation
Enjoyed our blog? Learn more about how Hut Six can help improve you security awareness with training and simulated phishing. Start a free trial now, or book a meeting with one of our experts.
Featured
5 Cyber Tips for your Business
Essential cyber tips for helping your business or SME improve information and cyber security.
The Benefits Of Maintaining Compliance For Your Business
By maintaining compliance for your business you can ensure operational efficiency, reduce financial risk, enhance public trust, engage your employees and realise your mission.
Top 5 Phishing Trends in 2022
Insights, trends, and statistics from the world of phishing in 2022.
10 Steps to Cyber Security
The main concepts of the Nation Cyber Security Centre's '10 Steps to Cyber Security' guidance.
Cyber Awareness Part II: The Psychology of Behaviour Change
Part two in our blog series examining how the psychology of behaviour change will help us deliver effective awareness campaigns.
5 Anti-Phishing Insights Every CISO Should Know
Based the latest scientific research, tips to reduce human error and protect businesses against phishing attacks.
Cyber Awareness Part I: The Psychology of Behaviour Change
Cyber awareness helps reduce human error and insecure behaviours. Examining how the psychology of behaviour change will help us deliver effective awareness campaigns.
Why Organisations Need an Email Security Policy
An email security policy is a document describing how an organisation's email system should, and most importantly, should not be used.
Human Error in Information Security
When Human Error is found in information security, it is often avoidable errors that allow much larger consequential problems to arise.
Investing in Information Security Awareness Training
Investing in Information Security Awareness Training - educating people against cyber threats should be considered essential for any organisation operating in 2021