The Psychology of Behaviour Change: Science, Behaviour & Social Influence
Part I: Science, Behaviour & Social Influence
At a time of mounting cyber-attacks, ransomware, and data breaches, information security specialists are understandably looking for solutions; many of which come in the form of technological interventions, such as firewalls or network monitoring.
Although these methods can be effective and should constitute a significant part of an information security strategy, the reality remains that human error is a contributing factor in an estimated 95% of all cyber incidents.
Reducing human error and insecure behaviour is a primary concern for any organisation or security specialist seeking to mitigate and reduce risk, with affecting meaningful behavioural change in users being the most challenging aspect.
Building a Practical Toolkit
This blog series seeks to analyse and explain some of the more practical and widely applied principles of behavioural science, as well as research from across different fields, specifically examining how this knowledge can be practically implemented to lessen insecure user behaviour in today’s information age.
In this first part, we will take a look at two of the most well established and applicable theories of behavioural change, a robust framework developed and used by the UK government, as well as the concept of social proof, or how it is social influences affect our security decision making.
“Human behaviour flows from three main sources: desire, emotion, and knowledge.” - Plato
Theories of Behaviour Change
Although there are several other popular behaviour change theories, both Social Cognitive Theory (SCT) and the Theory of Planned Behaviour (TPB) pertain most strongly to the research discussed later, and both are relevant to potential risk mitigation strategies.
Social Cognitive Theory
Developed in the 1960’s, Albert Bandura’s Social Cognitive Theory posits that the primary influences upon people’s behaviour are external and that learning occurs in a social context.
Asserting that human actions can be explained by an interaction of behaviour, personal and environmental factors; this model (shown below) is also known as reciprocal determinism.

According to Bandura, individuals do not adopt new behaviours solely by personally putting them to the test, rather they observe the behaviour of others and the results of those actions, and use this information to inform their own subsequent conduct.
Theory of Planned Behaviour
First proposed by Icek Ajzen in 1985, the Theory of Planned Behaviour suggests that behaviour is dependent on an individual’s intention to perform a behaviour. Intentions are determined by attitude (beliefs and values about the result of their prior behaviour) and subjective norms (beliefs about others’ thoughts or social pressure).

Illustrated above, TPB also asserts that an individual’s belief regarding their ability to perform a behaviour, plays a significant role in determining actions. This is called perceived behavioural control.
A Framework of Behaviour Change
There are many practices, principles and frameworks used within the field of behavioural psychology, though one of the most rigorous, widely used, and simple is MINDSPACE.
Commissioned by the UK’s Cabinet Office and developed by various leading experts, MINDSPACE seeks to explore “the application of behavioural theory to public policy for senior public sector leaders and policy-makers” and provide a theoretical basis for “low cost, low pain ways of ‘nudging’ citizens - or ourselves - into new ways of acting”.
Messenger - Who communicates information heavily influences our response. For example, security-related instructions would be more likely to influence change should it come from a chief information security officer (CISO) as opposed to a chief financial officer (CFO).
Incentives - Our response to incentives are reliably shaped by various biases and mental shortcuts (heuristics). For example, a message may be more or less effective depending on a loss vs. gain ‘framing’.
Norms – As social creatures, we are invariably influenced by the actions of those around us. Should we observe information security policy compliant (ISPC) behaviour in our co-workers, we ourselves are more likely to conform to these standards.
Defaults – Akin to ‘the path of least resistance’, pre-set or obvious behavioural paths are more appealing as they require less cognitive effort.
Salience – Novel and relevant information draws our attention. For example, should a security message appear more personalised or targeted (directed at a department or specific team), we are more likely to pay attention, as opposed to a more broad or generic audience (a whole company).
Priming - Actions are often influenced by sub-conscious cues, particularly with regards to our own perceived identity. A prime example of which comes from the Red Cross, who found that during a postal campaign seeking charitable donations, recipients were 30% more likely to give if they were reminded they had previously donated.
Affect - Emotional associations significantly impact our actions. For example, studies have found, “people in good moods make unrealistically optimistic judgements, whilst those in bad moods make unrealistically pessimistic judgements”.
Commitments – Consistent with Ajzen’s Theory of Planned Behaviour, people tend to try to be consistent with commitments, particularly when they are made public, since the breaking of the commitment can lead to reputational damage.
Ego – People typically act in ways that supports the impression of a positive self-image. A principle which is commonly leveraged against users in social engineering attacks which often appeal to generosity or feelings of sympathy.
Behaviour and Influence
Building upon these previously discusses theories, as well as the MINDSPACE framework, what are some well researched behavioural psychology observations we can actually leverage to promote secure behaviours?
Social Proof
In his 2006 book ‘Influence: The Psychology of Persuasion’, Professor Robert Cialdini examined some of the ways in which social influences shape our decision making.
Categorising individuals as either imitators or initiators, Cialdini posits that when the vast majority of us are confronted by a situation, we look to others for what the author terms ‘social proof’; a concept heavily aligned with SCT.
The equivalent of the MINDSPACE framework’s norms, this psychological phenomenon has been documented in several examples of information security-based research, including a 2014 experiment which sought to explore the effects of increasing the observability of secure behaviour.
With a sample of 50,000 Facebook users, researchers targeted individuals with various social proof framed messages (as well as a control message) designed to convince users to explore security features, examples of which are shown below.

The results of this experiment found that by simply showing people the number of their friends that used security features, users were 37% more likely to be enticed into exploring the promoted security features themselves.
Another example of the influence of social proof comes from a 2009 piece of research which found that internet users’ choices of software changed dramatically in relation to the total number of downloads.
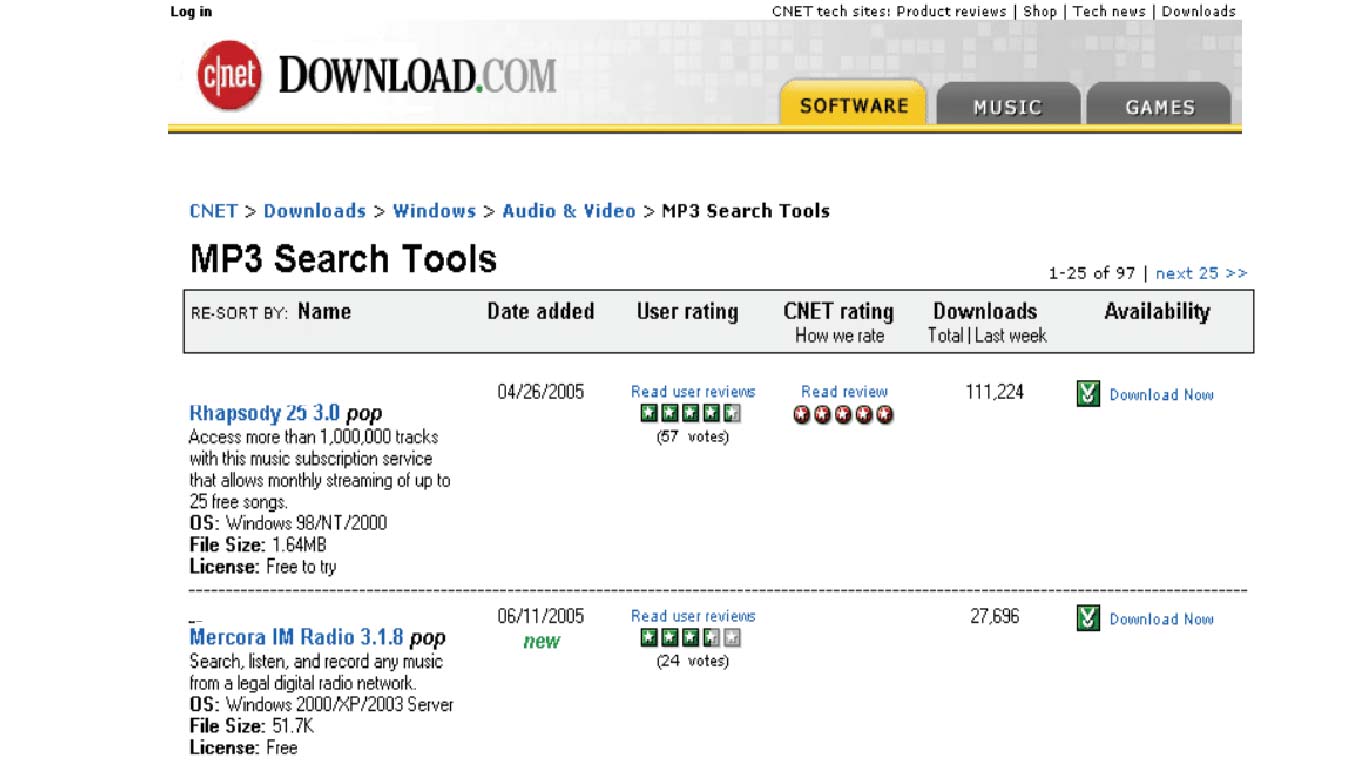
Demonstrating that users were likely to follow previous adopters’ choices, researchers also posited that the reliance on this metric may lead to inferior technologies being chosen; a finding which could have major implications when considering social proof in the information security context.
And finally, in a successful effort by Public Health England to reduce the over-prescription of antibiotics, behavioural change specialists implemented the technique (amongst others) of social influence in a letter sent to a group of the 20% highest prescribing GPs.
Included with the letter was the peer specific message: “the great majority (80%) of practices in London prescribe fewer antibiotics per head than yours”, evoking various MINDSPACE principles including messenger, norms, salience, and ego.
Compared to a randomised control group, GPs that received this simple intervention saw a subsequent fall in prescriptions by a statistically significant 3.5% and was heralded as both an effective and highly cost-effective method of behavioural change.
For those seeking to reduce the frequency of human errors and drive ISPC, the power of social influence (social proof) should not be underestimated, with multiple studies finding that providing information about the compliance of others increases the likelihood of users complying with security policies themselves.
Consider, in the context of implementing a company-wide security awareness training program, which of the following two communications are more likely to drive desirable action?
a) You can learn how to identify phishing emails by following this link.
b) 103 of your co-workers know how to identify phishing emails. You can also learn by following this link.
In part two we shall be further examining some of the concepts and discoveries that guide behavioural change experts in their work, including the use of deterrence or sanctions, principles of communication, and the evolving science of habit forming.
Security Awareness for your Organisation
Enjoyed our blog? Learn more about how Hut Six can help improve you security awareness with training and simulated phishing. Start a free trial now, or book a meeting with one of our experts.
Featured
Why Organisations Need an Email Security Policy
An email security policy is a document describing how an organisation's email system should, and most importantly, should not be used.
Human Error in Information Security
When Human Error is found in information security, it is often avoidable errors that allow much larger consequential problems to arise.
Investing in Information Security Awareness Training
Investing in Information Security Awareness Training - educating people against cyber threats should be considered essential for any organisation operating in 2021
How Secure is Microsoft Teams?
How Secure is Microsoft Teams? Information Security blog by Information Security Awareness solution provider Hut Six Security
Best Ways To Ensure Enterprise Data Regulation
Best Ways To Ensure Enterprise Data Regulation guest blog by technivorz.com and information security awareness solution Hut Six Security.
Writing a Disaster Recovery Plan
Writing a Disaster Recovery Plan: information security planning blog by information security awareness solution provider Hut Six Security.
What Policies Do I Need for a Security Program?
Security program policies blog by information security awareness training provider Hut Six Security.
Preparing for Cyber Essentials with Information Security Awareness Training
Security awareness training for Cyber Essentials blog by information security awareness training provider Hut Six Security.
Information Security Awareness Training in 2021
Information Security Awareness Training in 2021 blog by information security awareness training platform Hut Six Security
The Five Best VPNs for Work
What are the best VPNs for work? - VPN review blog by security awareness training provider Hut Six Security.










